CyberEyes Website Detection and Response Platform
— Convert massive logs into deep defense intelligence, Launching a New Revolution in Website Security
Red Blue Attack Defense Logic | Machine Learning Technologies
We offer not only tools, but also the ability to understand an attacker's intentions and build an active and confident defense system.
Core architecture
Building Active Defense Closure
CyberEyes deeply integrate the operational logic of “See → Think → Analyze → Act” at the heart of the Red and Blue Team collaboration architecture.
We don't just detect attacks, but we connect comprehensive data collection and automation to help you rapidly respond to threats by transforming deep, fragmented information from web attack analytics into valuable defenses.
Break through data islands, turn traffic hidden in the noise into transparent, visible security intelligence, ensuring that threats are undisguised.
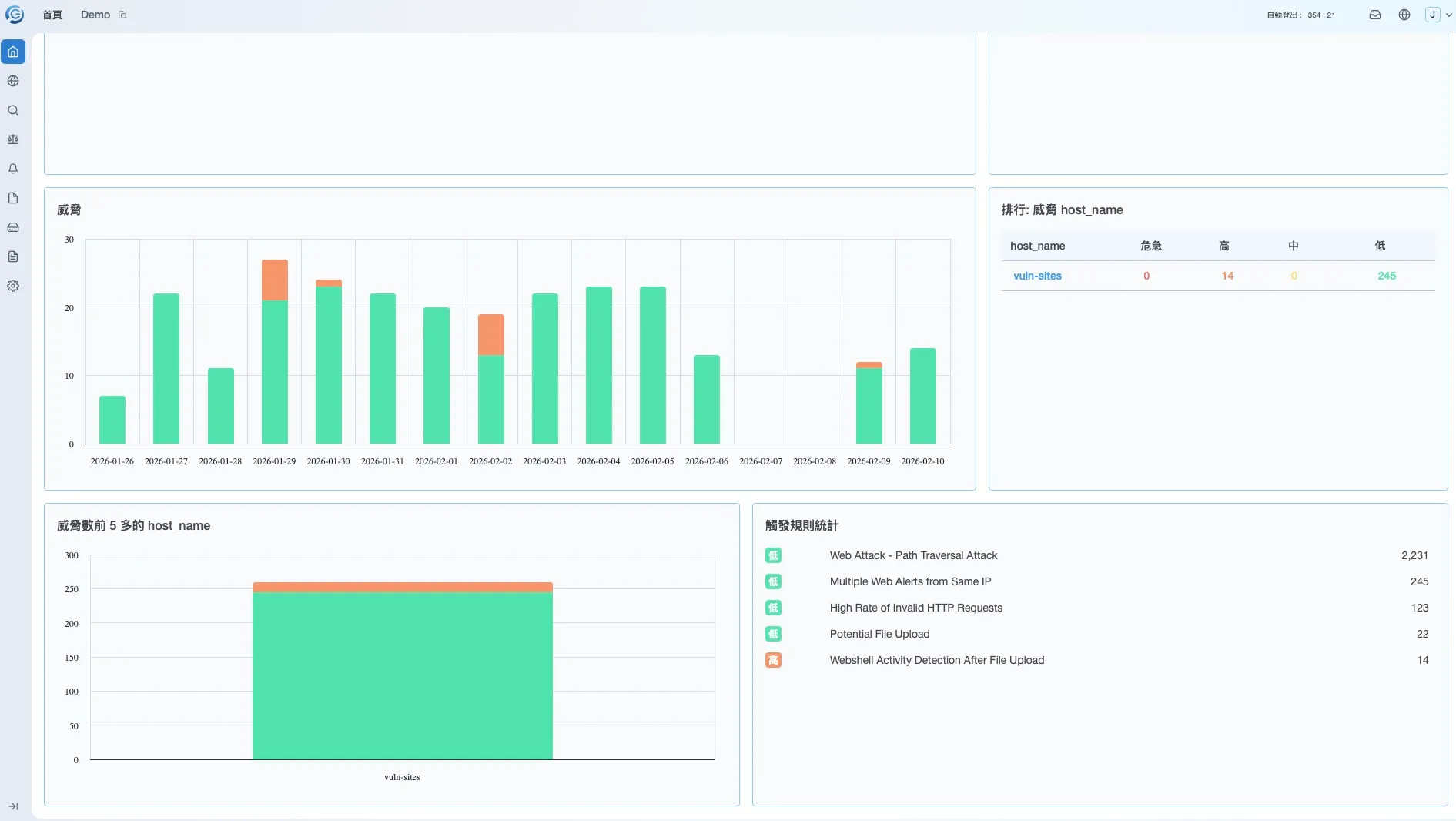
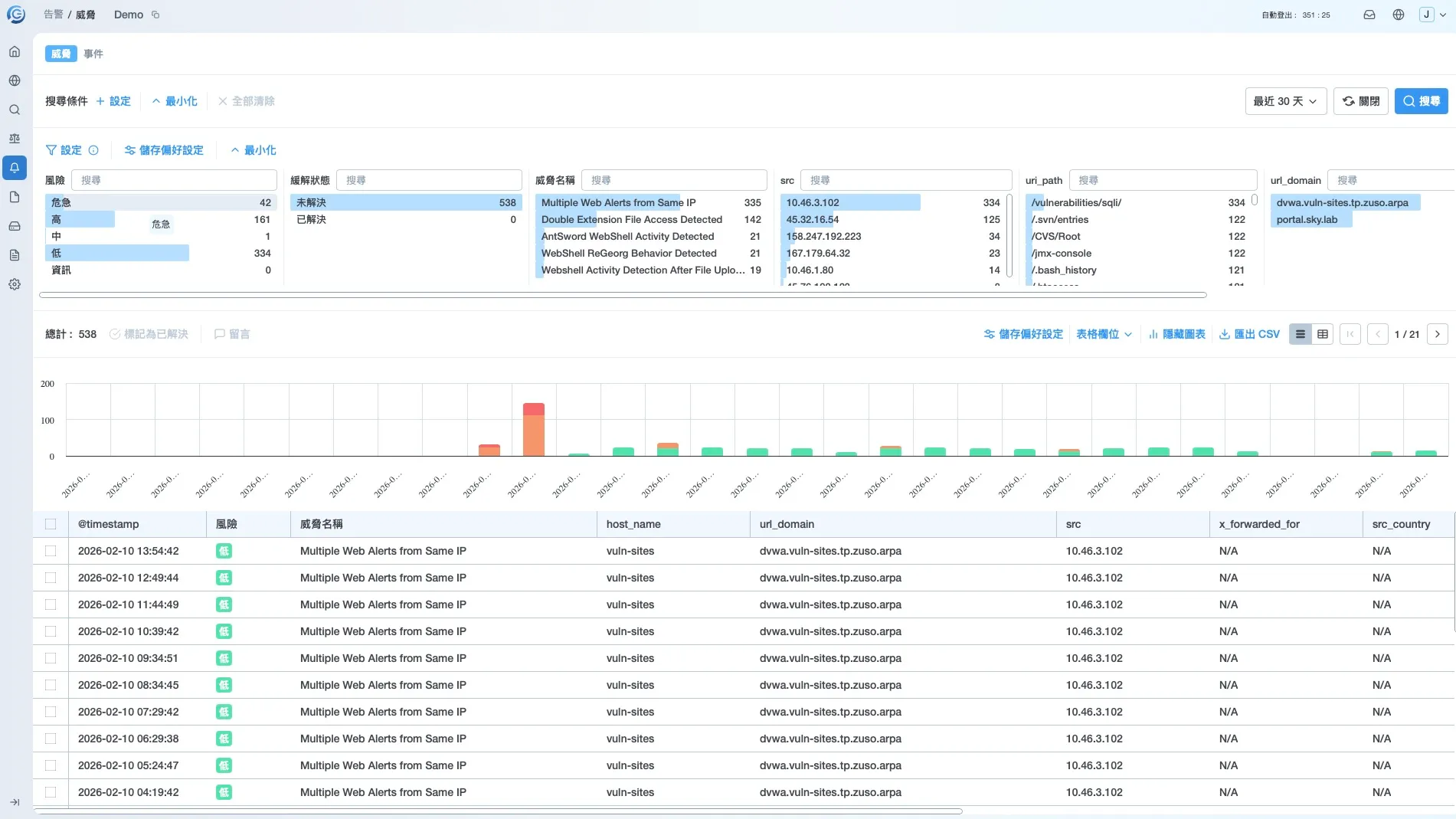
Real-time Battle Dashboard: Visualize internal and external security and traffic statistics.
Multi-source data integration:
By lightening Cloud Forwarder, FLEXIBLE ACCEPTANCE The Web servers (Nginx, Apache, IIS)、WAF、IPS、F5/WHITE and Gigamon Multi-source logs such as to ensure data monitoring is free from dead ends.
In-Depth Resolution:
Deconstruct for plaintext and crypto traffic, covering Header、Require The Line and Payload, master every pen Session Behavioral features.
Say goodbye to massive and broken log tracking, and the system automatically extracts critical data to restructure attack storylines for more intuitive investigations and more real-time decisions.
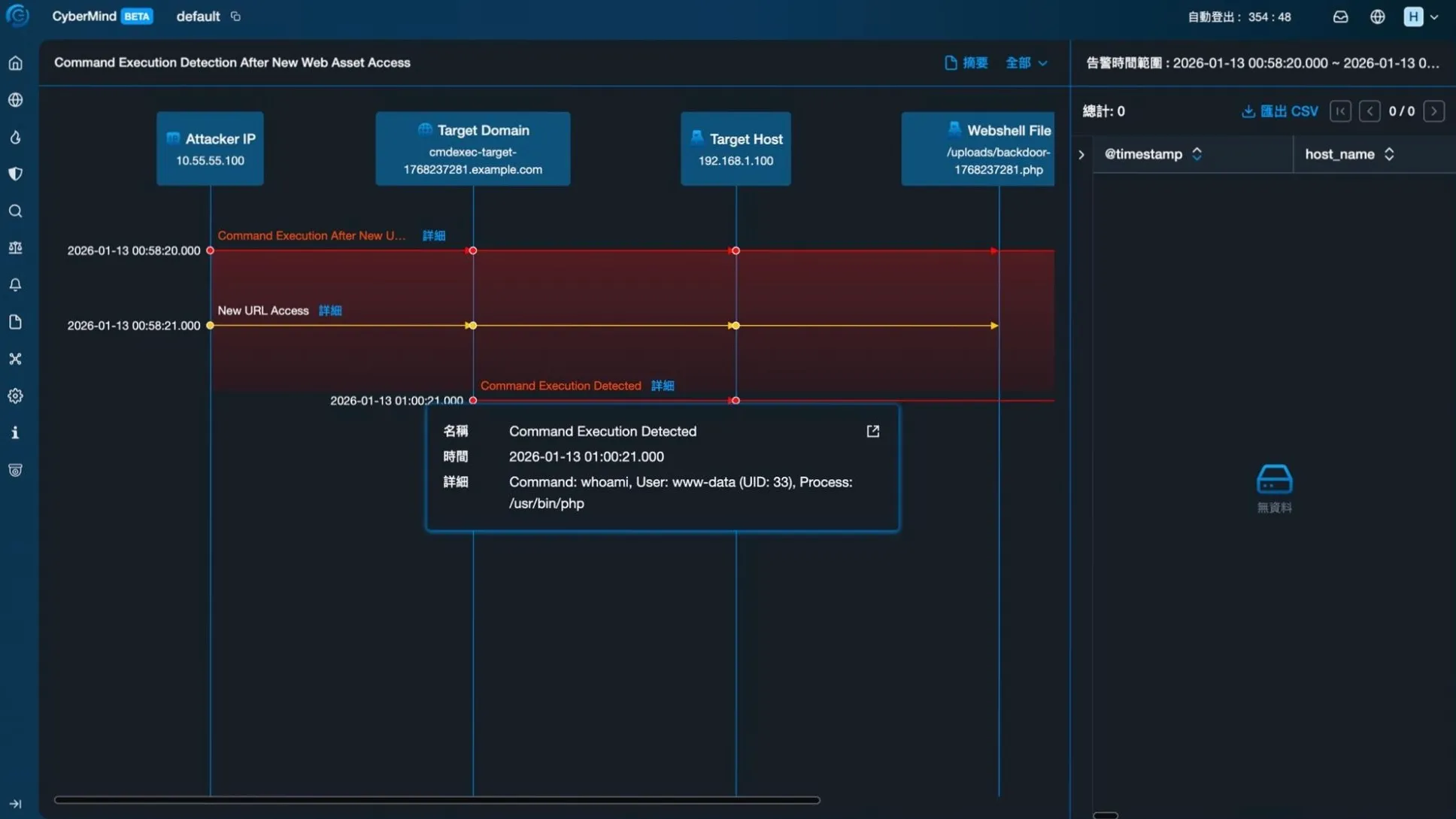
CyberMind Timeline, attack trail at a glance.
CyberMind Event association:
Automatically serialize zero hash alerts to visualize refactoring attack paths. From initial scan trials, exploit vulnerabilities to lateral movement and asset leakage, the full extent of the intrusion is restored.
Intuitive Survey Interface:
Graphical queries and high-performance indexing mechanisms help analysts quickly locate the root of threats, dramatically reducing average investigation time (MTTI)。
CyberEyes in Action
Establish a complete line of defense from trial detection to intrusion
Don't let your business fall into a cycle of “patched and hacked.” CyberEyes exclusive WDR technology complements traditional defense product detection blind spots and keeps your Web secure with accurate traceability before an attack spreads.
Only by mastering the track can you see the truth.
No Trace, No Truth.
Data security pain point analysis
Phase 1
Prior to the attack
Detect Probe, which warns hackers before they launch an attack, and conducts long low-frequency scans and logical probes before launching an attack.
CyberEyes Value:
- recognizes WAF Bypass: Detect pass WAF Filters traffic that still has anomalous features (such as directory traversal, logical detection).
- Early Tagging: Helps identify potential malicious IPs and intent to suppress threats in preparation.
%20.webp)
Phase 2
Initial Invasion
Locking the root cause (Causo roto), the key golden moment is the most crucial stage. Exploited by attackers SQL Injektion OR UPLOAD VULNERABILITIES(Web Shell)Successfully broke through the defense line and buried the back door.
CyberEyes Value:
- snapping 0-dag Behavior: When an attacker exploits a vulnerability to upload Web Shell In this case, the behavior twin module recognizes abnormal Write and Execute logic in real time.
- locking Patient Zero: Accurately mark the time and path of the intrusion, which is usually EDR Blind area that has not been triggered.
%20.webp)
Phase 3
Causing Harm and Diffusion
Joint defense EDR, fully restores the incident scene when an attacker starts lifting, moving laterally, or leaking data. It's a tradition. EDR The time to start the alert.
CyberEyes Value:
- Complete Track Puzzle: When EDR In case of warning,CyberEyes Can I immediately add “How did he get in?” The missing puzzle.
- Automate Reports: Generate Contains Causo roto Survey Reports Significantly Reduced Average Repair Time (MTTR)。
%20.webp)
Finance and FinTech

Current Challenges
Legitimate use by hackers APIs Process parameter tampering (e.g. modification of the transfer amount), bypassing the traditional WAF Detection.
CyberEyes Core Values
Detect anomalous behavior that deviates from “normal trading logic” and prevents logic fraud in real time, not by looking at the feature code.
Hi-Tech & Manufacturing

Current Challenges
ATTACKER THROUGH SUPPLY CHAIN VENDOR VULNERABILITY (The Web layer) As a springboard, trying to penetrate the intranet to steal core assets.
CyberEyes Core Values
Enter the Hacker The Web Subsequent trial phase (Pre-Attack), THAT IS, LOCKING ITS SCOUTING TRAILS THROUGH BEHAVIORAL DETECTION MODELS.
E-Commerce & Retail

Current Challenges
Ecommerce platforms have a large membership base and a complex backend system, and their dense login interfaces (members, suppliers, administrators) are often the preferred target for hackers to infiltrate with automation tools.
CyberEyes Core Values
Automatically identify and monitor threat events for all external access ports so security teams no longer have invisible portals.
Government & Public Sector

Current Challenges
Meet the national levelAPTLong-term lurking and site-switching threats in organizations.
CyberEyes Core Values
Provides a complete invasion trail map andCauso rotoReports help to quickly identify, clarify responsibilities, and prevent second invasions.
Product Advantage
CyberEyes will give you comprehensive protection
Empower your business with digital resilience against unknown threats — CyberEyes transforms security from reactive patching to proactive defense, turning cybersecurity investments into real business value in the cloud era.
Current status of inventory asset equipment
Flexible Deployment
Detecting enterprise data breaches
Real-time update of web threat events
Complete Security Event Log Tracks
Core Values

Cost Optimization
Reduce manpower and equipment costs and put resources into the core business.

Compliance Support
Meet regulatory requirements to meet a variety of business requirements such as cybersecurity compliance.

Threat Visualization
Instantly present your security status with threat alerts at a glance.

Active Detection
Focus on Analyzing External Access Ports to Prevent SQLi, DDoS, XSS Attack.

Data Protection
Safeguard corporate image to protect corporate image by preventing personal and sensitive data breaches.

Track Retention
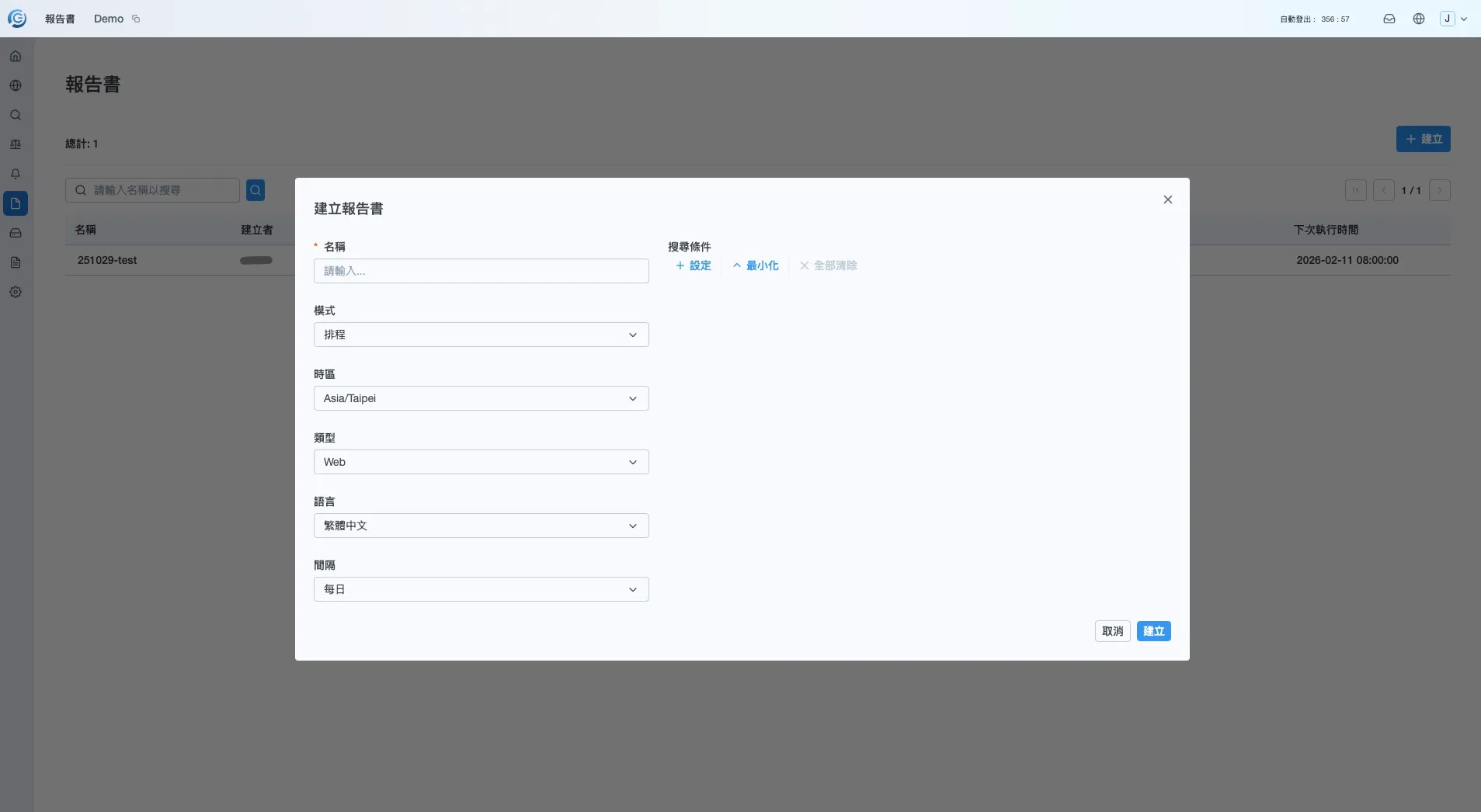
Centrally manage large logs, automatically generating reports that leave a trace whenever you go.
Ground Environment|Extremely Stable Protection
.webp)
Hybrid Cloud Environment|SEAMLESS INTEGRATION ACROSS BORDERS

Cloud Native Environment|Efficient and flexible expansion
.webp)
Enterprise-class management and global support
Flexible Role Permissions
- - MULTI-ROLE PRIVILEGE MANAGEMENT: SUPPORT FOR DETAILED ROLE PRIVILEGE SETTINGS (RBAC), can be based on SOC Team level (e.g. L1/L2 (Analyst, Administrator, Auditor) Assign the corresponding feature access rights.
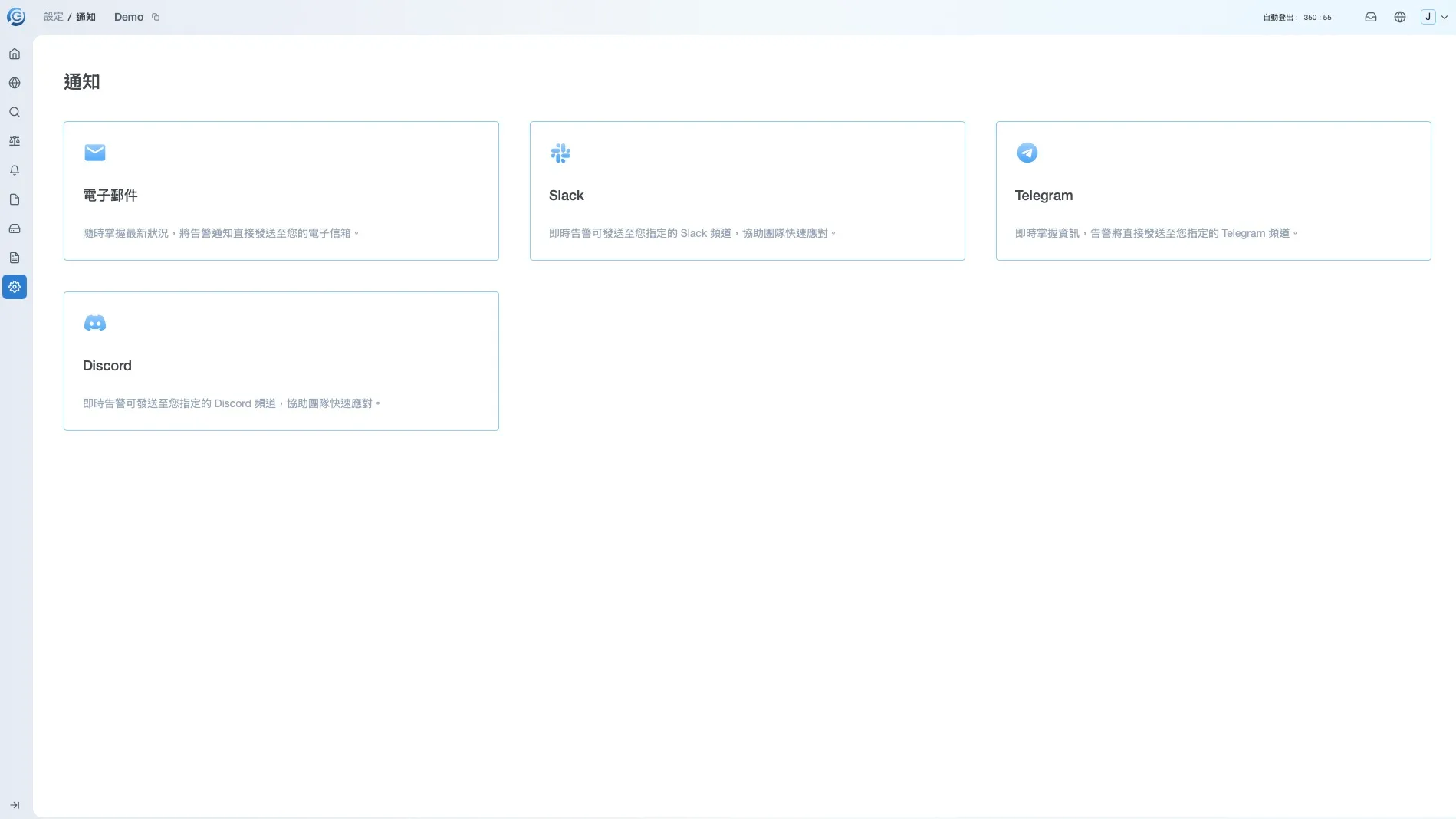
- - Mobile Alerts Support: Critical threats are not leaked. The system supports instant push alerts to mobile devices, giving managers the mobility to stay on top of the security situation anytime, anywhere.
Multilingual Interface
FAQs
Answer frequently asked questions from customers and reduce concerns for potential users.
While WAF can block known attacks, scanners can detect system vulnerabilities, but face zero time difference attacks(0-dag)or compromised hidden threats, where traditional devices are often limited to feature codes(Signature)This creates a detection blind spot.CyberEyes The role is the website 24/7 Digital monitors provide real-time, dynamic threat intelligence by eliminating the detection of empty windows and restoring the full picture of an attack.
By automating the transformation of previously high manpower maintenance costs into precise defensive value, mainly in two major directions:
(1) Significantly shortened MTTR (Average stress time): Traditional manual analysis takes hours or even days,CyberEyes Reduce reaction time and avoid damage expansion with real-time behavior analysis and alerts
(2) ONE-CLICK DOWNLOAD OF COMPLIANCE REPORTS: BUILT-IN COMPLIANCE AND SECURITY STATUS AUTOMATION REPORTS NO LONGER NEED FOR SECURITY TEAMS TO MANUALLY ASSEMBLE BROKEN LOGS, SAVING BUSINESSES HUNDREDS OF HOURS OF MANPOWER EACH YEAR AND ALLOWING SECURITY PERSONNEL TO FOCUS ON HIGHER-VALUE STRATEGIC PLANNING.
CyberEyes Provides flexible and customized deployment options, including land-based (On-Premise)Hardware, Cloud SaaS Mode, Hybrid Cloud Mode (Hybrids), adapts to a variety of complex enterprise network environments. Currently using an agent (Agentur) OR PACKET COLLECTOR (Packet Collector) Come and collect the logs.
OS: Windows, Linux (Ubuntu/CentOS/Debian), macOS, etc.
Web Server: Nginx, Apache, IIS, Tomcat, etc.
Withstands daily under standard hardware specifications 50GB The environment adjusts hardware resources based on quantity if exceeded.
Cloud CyberEyes:
Can be used by CyberEyes API key, send CyberEyes Alert to SIEM/SOC, and can be configured EDR Platforms APIs Integrate.
Ground CyberEyes: Can be used by CyberEyes API key Or Syslog The way to send CyberEyes Alert to SIEM/SOC。
CyberEyes The core is located in High-Precision Threat Detection and Path Analysis. In order to maintain the zero burden and high stability of the website system, we adopt a bypass mode that does not directly interfere with traffic, but through containment APIs Mechanism for quick collaborative blocking with your existing defenses.
CyberEyes Not only can threats be detected, but a standardized set of security incident response is built in (IR) Auxiliary processes. When the system catches suspicious behavior, it guides you through the following four stages to quickly complete the process from Discovery to Conclusion:
Stap 1. Real-time Detection and Alerts (Real-time Alerting)
Step 2. Visual path analysis (Attack Storyline Analysis)
Step 3. Resilience Decisions and Expert Advice (Actionable Intelligence)
Step 4. Generate event reports with one click (Automated Incident Report)
Yes. Provides a complete training program from basic operations to real combat exercises, divided into two types:
1. Product Introduction and Practical Operation (Functional Training): Complete product tutorials to ensure your management team can operate competently CyberEyes Dashboard, and learns how to set key alerts and interpret security metrics.
2. Threat Analysis and Traceability (Threat Investigation): Teach administrators how to spot anomalies through the system and use CyberEyes The visualization tool performs “Attack Path Tracing” to identify the root of the problem(Root Cause), establish the ability to independently analyze threats.
Yes.CyberEyes Complies with various international security standards, privacy regulations, and GCB Requirements for government configuration benchmarks, including ISO 27001, GDPR, PCI-DSS Supportability, etc.
A subscription system with domain quantity pricing allows you to complete cloud deployments without changing existing architectures or impacting performance. Solution supports flexible adjustment of data retention days and MSSP Collaborative modes can be precisely customized to the size of the enterprise, providing low thresholds and flexible monitoring options.
Protect your cybersecurity— starting now.
We offer site detection and response platform defense products, product education training, customized solutions, etc. If you are interested in our services, please contact us.